Despite what you might think, not all computer hackers are bad. Some companies hire people to hack into their computer networks to expose weaknesses, vulnerabilities and security holes. This is considered "ethical hacking," and you can make a career out of it if you're good at it. Here's an overview of what you need to know to become a hacker, including what are considered to be the essential skills to becoming a hacker.
Hacker Duties and Specializations
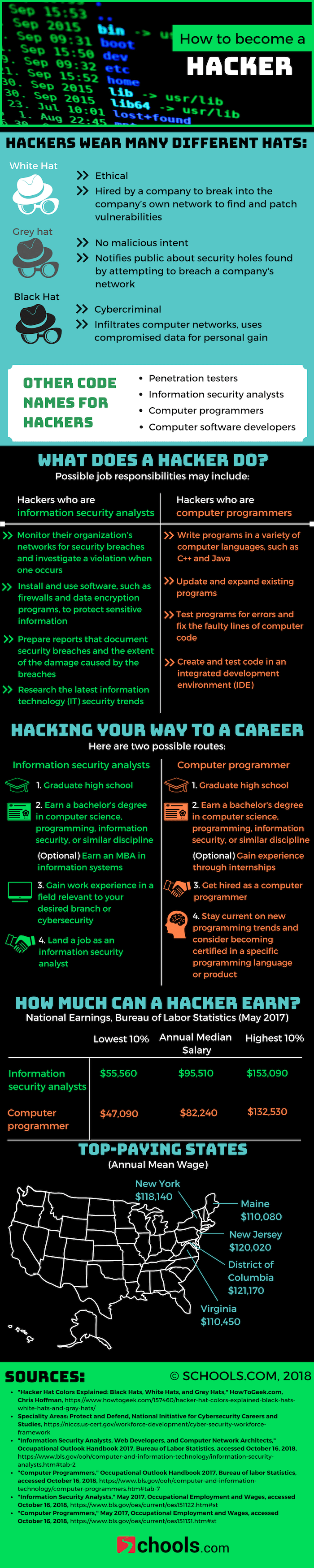
What you do in this career depends entirely which kind of hacker you are. If you're a hacker who's an information security analyst, your day-to-day tasks might include:
- Monitoring computer networks and systems for security breaches
- Making security recommendations
- Creating security policies for a company, such as a disaster recovery plan
- Researching cyberthreats
If you're a hacker whose specialty is computer programming, then your hacking responsibilities might involve:
- Writing computer software with programs such as C++ and Java
- Checking applications for bugs and rewrite code if there are any
- Helping design programs
You can also be an ethical hacker apart from being an information security analyst or computer scientist, as long as you fit the definition of an ethical hacker. Which is, according to Lexico, "A person who hacks into a computer network in order to test or evaluate its security, rather than with malicious or criminal intent." In this vein, you might also see the job of an ethical hacker referred to as a white hat hacker or a penetration tester.
For grey hat hackers who work without malicious intent to serve as a watchdog of sorts, hacking basics could involve notifying the public of a company's network security holes. Black hat hackers are cybercriminals who infiltrate computer networks and use compromised data for personal gain.
How to Become a Hacker
- Acquire essential hacking skills and learn about the best programming language for hacking by completing a four-year degree program in a relevant tech field. While there aren't really "hacking degrees," many who want to become hackers go the route of information security analysts or computer programmers. Bachelor's degree programs related to hacking can include one of the following:
- Computer science degree programs
- Computer programming degree programs
- Information security degree programs
- Computer information technology degree programs
- Intern or gain experience through an entry-level job as a computer programmer or information security analyst.
- Enhance your hacking skills by taking courses or earn certifications in ethical hacking, such as those offered at EC-Council.
Ethical Hacker Salary and Career Outlook
Whether you become a hacker via a career as a computer programmer or information security analyst can determine your salary and job growth. Here's an idea of what to expect for either starting point at the national level:
| Career | Total Employment | Annual Mean Wage | Projected Job Growth Rate |
|---|---|---|---|
| Computer Programmers | 199,540 | $92,610 | -7.2% |
| Information Security Analysts | 125,570 | $104,210 | 31.6% |
No matter which route you take, ethical hackers serve a vital role to the computer and business world, along with many other industries such as healthcare. It can be a great job to pursue if you're interested in both computers and public service. For more information, explore the visual guide to becoming a hacker below.
- Certified Ethical Hacker, EC-Council, http://www.eccouncil.org/Certification/certified-ethical-hacker
- Computer Programmers, Bureau of Labor Statistics, Occupational Employment Statistics, U.S. Department of Labor, http://www.bls.gov/oes/current/oes151131.htm
- Information Security Analysts, Occupational Employment Statistics, Bureau of Labor Statistics, U.S. Department of Labor, http://www.bls.gov/oes/current/oes151122.htm
- Computer Programmers, "Occupational Outlook Handbook, " Bureau of Labor Statistics, U.S. Department of Labor, http://www.bls.gov/ooh/computer-and-information-technology/computer-programmers.htm#tab-6
- Information Security Analysts, "Occupational Outlook Handbook, " Bureau of Labor Statistics, U.S. Department of Labor, http://www.bls.gov/ooh/computer-and-information-technology/information-security-analysts.htm#tab-6
- Ethical Hacker definition, Lexico, a collaboration between dictionary.com and Oxford University Press, https://www.lexico.com/definition/ethical_hacker